Accordingly, by taking advantage of user trust in familiar services with the same domain @google.com, attackers can overcome the traditional email security layers of the system, thereby increasing the effectiveness of the scam campaign.
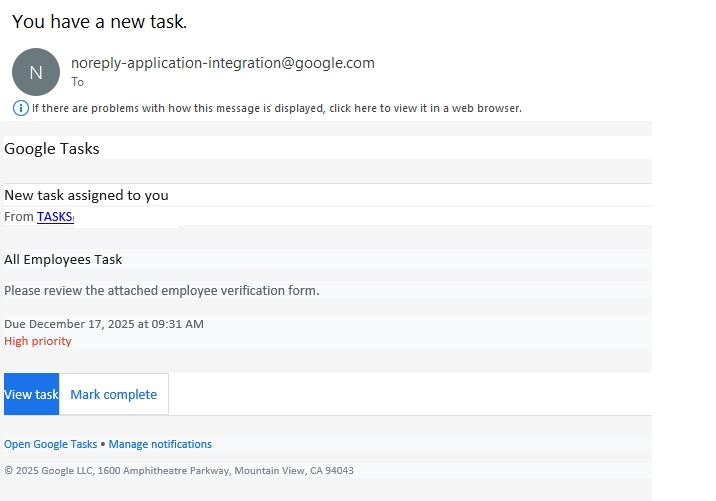
Notably, in this campaign, under the guise of a notification with a completely valid interface from the Google Tasks work management application with the title "You have a new task", victims easily believe that this is an official work request.
The content of the notification creates the feeling that their business has assigned a task through a tool from Google, thereby putting pressure on the recipient to quickly follow the instructions. To increase persuasiveness, the notification is often associated with a high priority level and a deadline for urgent processing, aiming to hit the recipient's rush and make them respond quickly without time to verify.
Specifically, as soon as you click on the attached link, the victim will be redirected to a fake form disguised as a "employee verification" page. Here, under the name of identity verification, the victim is required to provide login information to the business account.
Once falling into the hands of the attacker, this login information can be exploited to illegally access the internal system, steal data or serve as a springboard for subsequent attacks targeting businesses.
Mr. Roman Dedenok, an analyst and anti-spam expert at Kaspersky, said: "Google's vast service ecosystem is being exploited by fraudsters for many bad purposes. The trick of exploiting Google Tasks is just part of a trend that has been recorded before and is expected to continue until 2026, when cybercriminals are constantly taking advantage of legitimate platforms to spread fake content and other online scams.
Under the guise of official domain names, these notifications often easily overcome many layers of spam filters and anti-fraud. At the same time, the socio-technical factor - when everything is staged as an internal process of the business - further makes victims lose vigilance.
Recommendations
To respond to this form of attack as well as similar threats, Kaspersky's cybersecurity experts recommend:
- Be careful with invitations or notifications of unclear origin from any platform, even if they appear to be sent from a reliable source.
- Check the URL carefully before clicking on the link.
- Do not call according to phone numbers provided in suspicious emails. In case you need to contact the support department, users should find the official phone number on the homepage of the corresponding service.
- Report suspicious emails to the platform provider and activate multiple-factor authentication (MFA) for all accounts.
- For business users, using solutions with multi-layered defense mechanisms, supported by machine learning algorithms, brings strong protection against increasingly sophisticated threats, helping businesses proactively respond to increasing cybersecurity risks.
- For individual users, they should use solutions that provide anti-fraud features of AI applications, designed to support preventing fraudulent attacks and improve overall security level.











