Supply chain attack
According to a survey conducted by Kaspersky, in the past 12 months, 31% of businesses globally have been affected by supply chain attacks, higher than any other type of cybersecurity threat. This attack method is also common in the Asia-Pacific region (APAC).
In China, 2/5 of the total number of businesses facing supply chain attacks in the past year, 9% higher than the global average and leading the region. Followed by Vietnam (34%), India (29%), Singapore (26%) and Indonesia (20%).
Supply chain attacks specifically target organizations with high levels of connectivity. Large-scale businesses recorded attack rates of up to 36%, significantly higher than small and medium-sized businesses.
Attacking through trusted relationships
In the past year, the form of attack exploiting trust relationships was in the top 5 most common cybersecurity threats, affecting 25% of businesses globally. In the Asia-Pacific region, Singapore is the most affected market, followed by Vietnam, India, Indonesia...
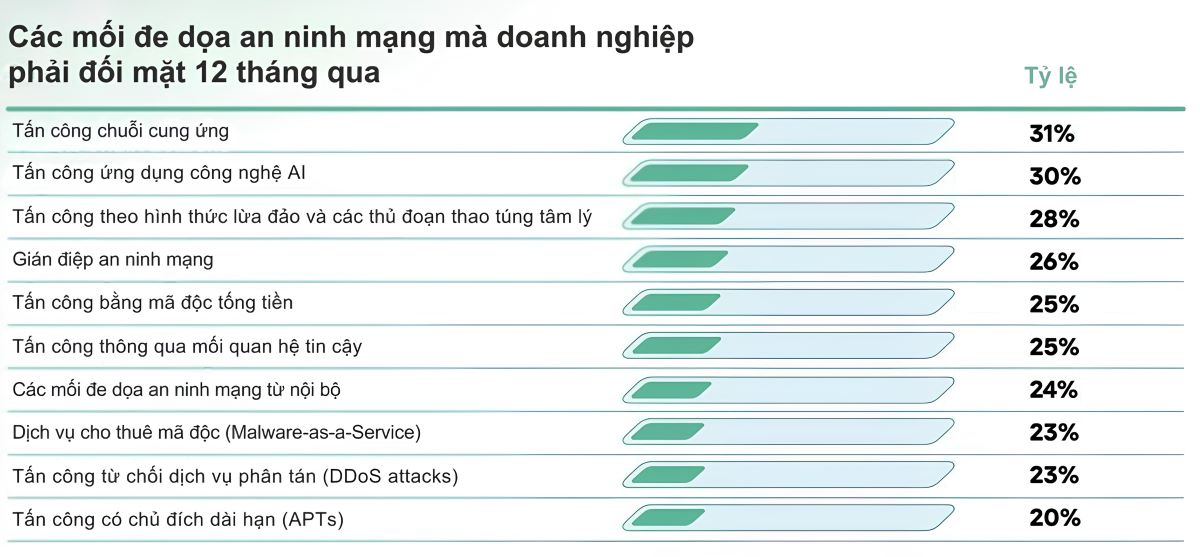
Although supply chain attacks and relationships-based attacks are among the most common threats, surveys show that many business leaders still tend to underestimate these threats.
When asked to classify threats by level of danger, instead of focusing on the types of attacks that businesses face the most, organizations often focus on complex forms of attacks such as long-term targeted attacks (Advanced Persistent Threats - APT), ransomware or insider threats.
Recommendations
To minimize cybersecurity risks related to supply chain attacks, experts have given advice:
- Carefully evaluate the provider before signing a cooperation agreement. Check network security policies, information about previous incidents and compliance with industry security standards. For software and cloud services, additional vulnerability data and intrusion test results should be considered.
- Establish network security terms in the contract. Conduct periodic security audits and ensure that the provider complies with security policies as well as the organization's incident notification process.
- Apply preventive technology solutions. Implement security principles such as least privilege, zero trust, and strict identity management, to minimize damage if suppliers are attacked by bad actors.
- Ensure continuous monitoring. Use solutions such as XDR or MXDR to monitor infrastructure in real time. Thereby, promptly detect abnormalities in the software as well as network traffic, depending on the operating capacity of the internal team.
- Develop an incident response scenario. Ensure a comprehensive response plan for supply chain attacks, including quick steps to identify and isolate the source of infection - such as temporarily disconnecting the supplier from the internal system.
- Strengthen cooperation with suppliers on security issues. Strengthen defense capabilities and consider this a common priority for both sides.











